This week, I was privileged to showcase the work of the whole team on Moscone's stage for the RSAC LaunchPad.
There's no winner at LaunchPad and that's not the point. The point is that a small team and a product built in the trenches with customers, got to stand in front of the security industry and make the case for something we believe deeply: the way we manage vulnerabilities is broken, and it's time to fix it.
The Zero-Day clock is ticking. VM Programs need to be reinvented.
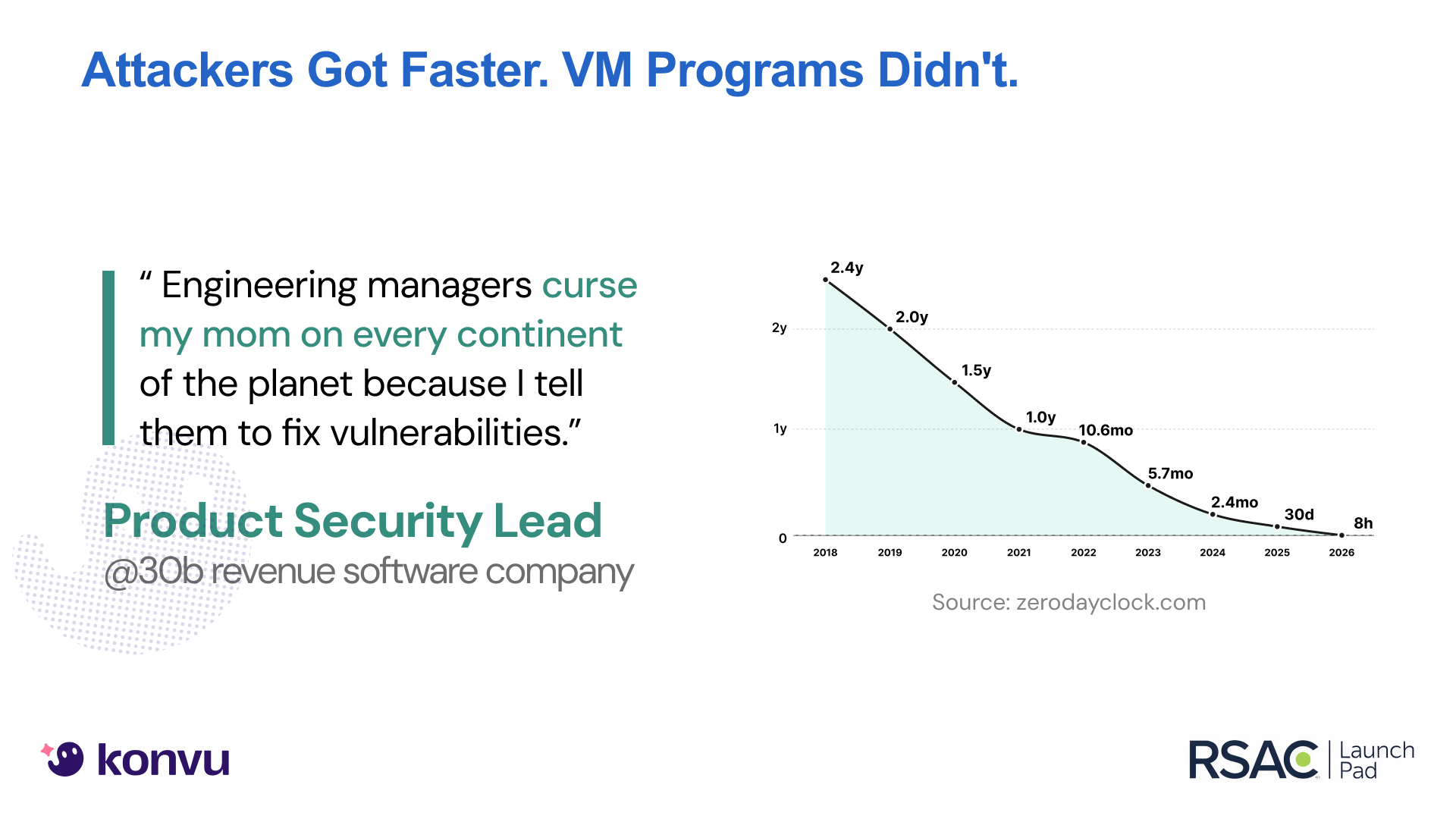
Attackers used to take weeks to exploit new vulnerabilities. That timeline is trending toward hours — look at Zero Day Clock to get a visceral sense of how tight that window has become. The entire vulnerability management market was built for the old speed. Tools, workflows, programs: none of it works at the pace attackers move today.
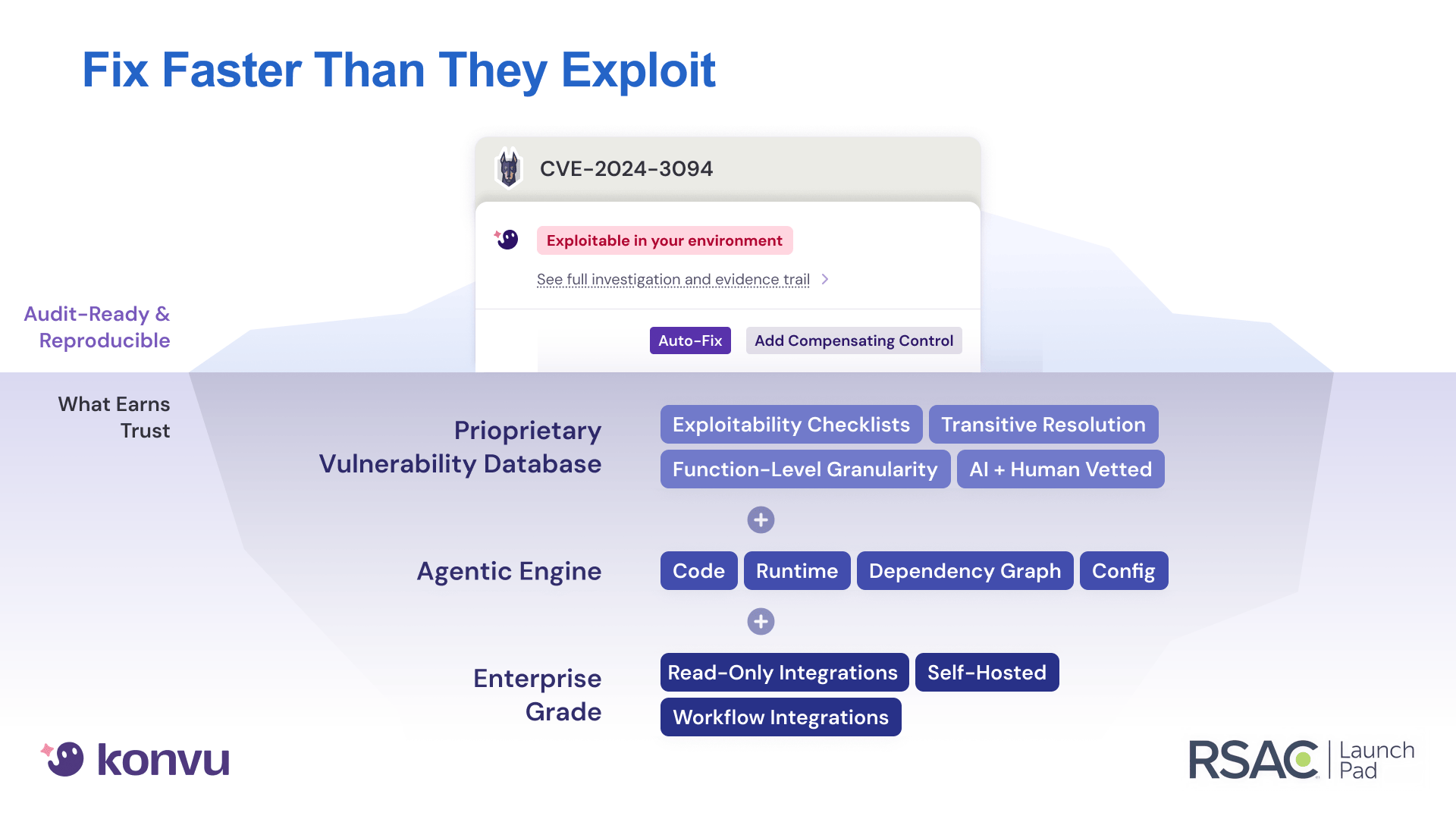
Konvu is an agentic vulnerability management product that sits on top of your existing scanners and answers the question security teams actually need answered: can this vulnerability be exploited in my environment? Not "is this a critical CVE." Not "is this exploited in the wild." But: is this actually exploitable given your specific context? And when it is, we suggest a fix or a compensating control.
We do this with a proprietary vulnerability database, built by dedicated agents and human-vetted. For every CVE, we know the specific conditions that make it exploitable. An agentic engine then takes those conditions and autonomously investigates each one against your actual environment — your code, your configuration, your runtime — to deliver a verdict with a full evidence trail. It's the combination of proprietary data and autonomous agentic investigation that makes real exploitability verdicts possible, and neither layer can be shortcut.
90% noise reduction in Enterprise environments
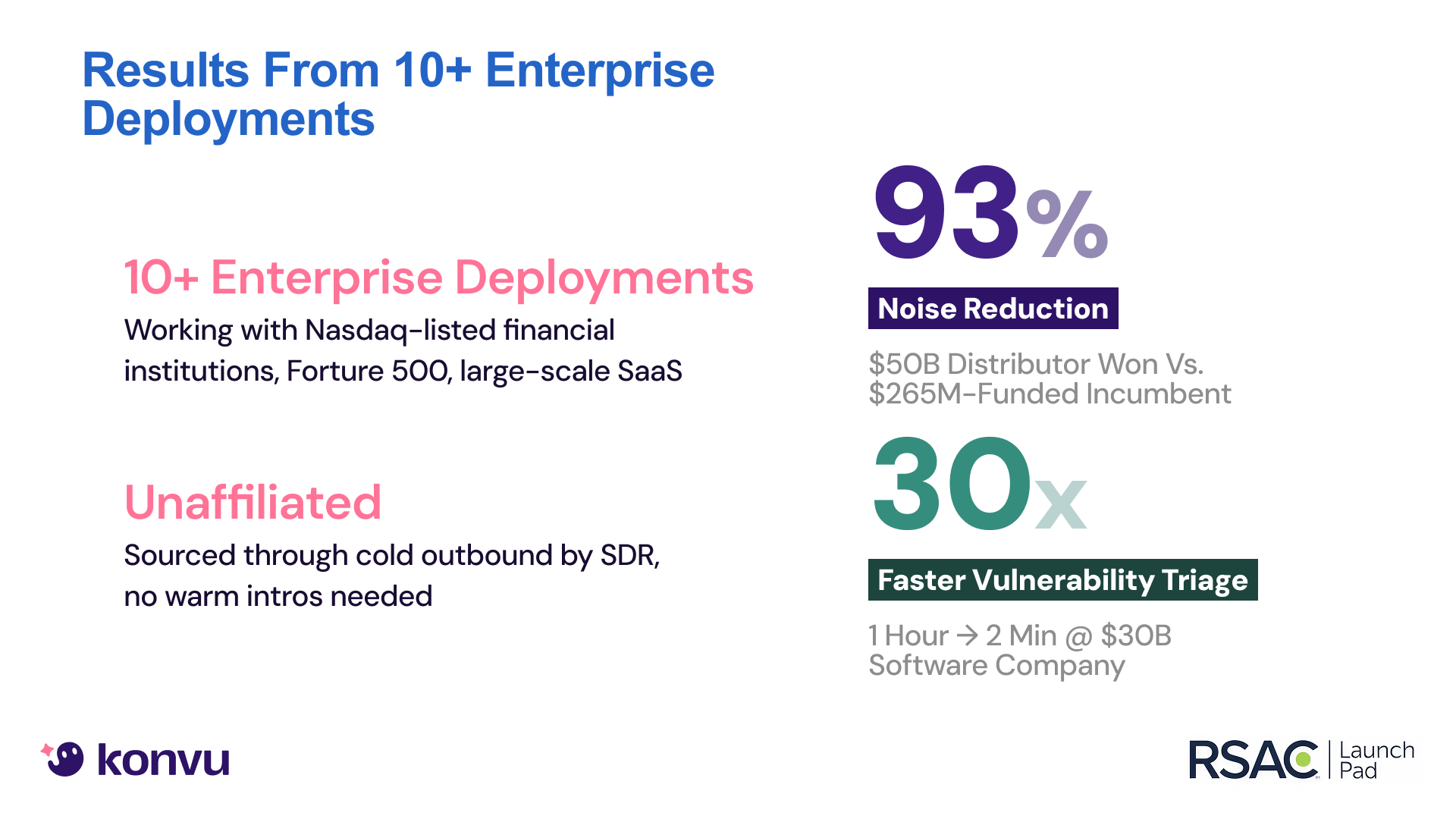
I want to be direct about this: the reason we were on that stage is our early customers.
Every early customer who gave us access to their environment, pushed back on our verdicts, told us what mattered and what didn't, they shaped Konvu into what it is today. Reducing alert noise by 90%+ in real production environments. Building trust with engineering teams who had given up on their security tooling.
To the security and engineering teams at our early customers: thank you. You took a bet on a small team with a big thesis, and you held us to a high bar. That's exactly what we needed.
SAST Triage and Auto-Fix in beta
The LaunchPad pitch captured a moment, but the product hasn't stood still. In the last few weeks, we've released in beta:
- SAST Triage: the same exploitability analysis that powers our SCA triage, now applied to static analysis findings. Same principle: filter to what actually matters, provide the evidence trail.
- Auto-Fix: for the vulnerabilities that are confirmed exploitable, Konvu now researches the safest remediation path, generates validated pull requests, and runs them through your CI pipeline before a developer ever sees them. No more broken Dependabot PRs for vulnerabilities that don't even matter.
These aren't incremental features. They represent the full loop we've been building toward: detect what's exploitable, prove it, and fix it. Autonomously.
The team behind it
I'm biased, but I think we've built something rare. A team of hungry, diverse engineers who push each other. People who chose a hard problem at an early stage because they wanted to build something that matters.
I'm proud of this team. LaunchPad was their moment as much as anyone's.
What's next
Time-to-exploit is trending toward zero. The industry needs tools that move at attacker speed, not audit speed. We're glad to be contributing to that shift.
We're heads down. More customers to onboard, more capabilities to ship, more of the vulnerability management workflow to rethink. If you're a security leader frustrated with alert fatigue and remediation backlogs, we'd love to talk.
And if you were at RSAC this week, thanks for the energy. It was a good week.