SOC 2 Type II certified
Independently audited by Johanson Group. Full report available via our Trust Center.
Self-hosted option
Our K8s controller runs in your environment. Konvu never has access to your code.
Zero LLM data retention
Contractual zero-retention agreements with all LLM providers. No training on your data.
Annual external pentests
Independent third-party penetration testing of our infrastructure and application.
Choose your deployment model
Both models minimize data exposure by design. The difference is where code analysis runs.
Self-hosted analysis
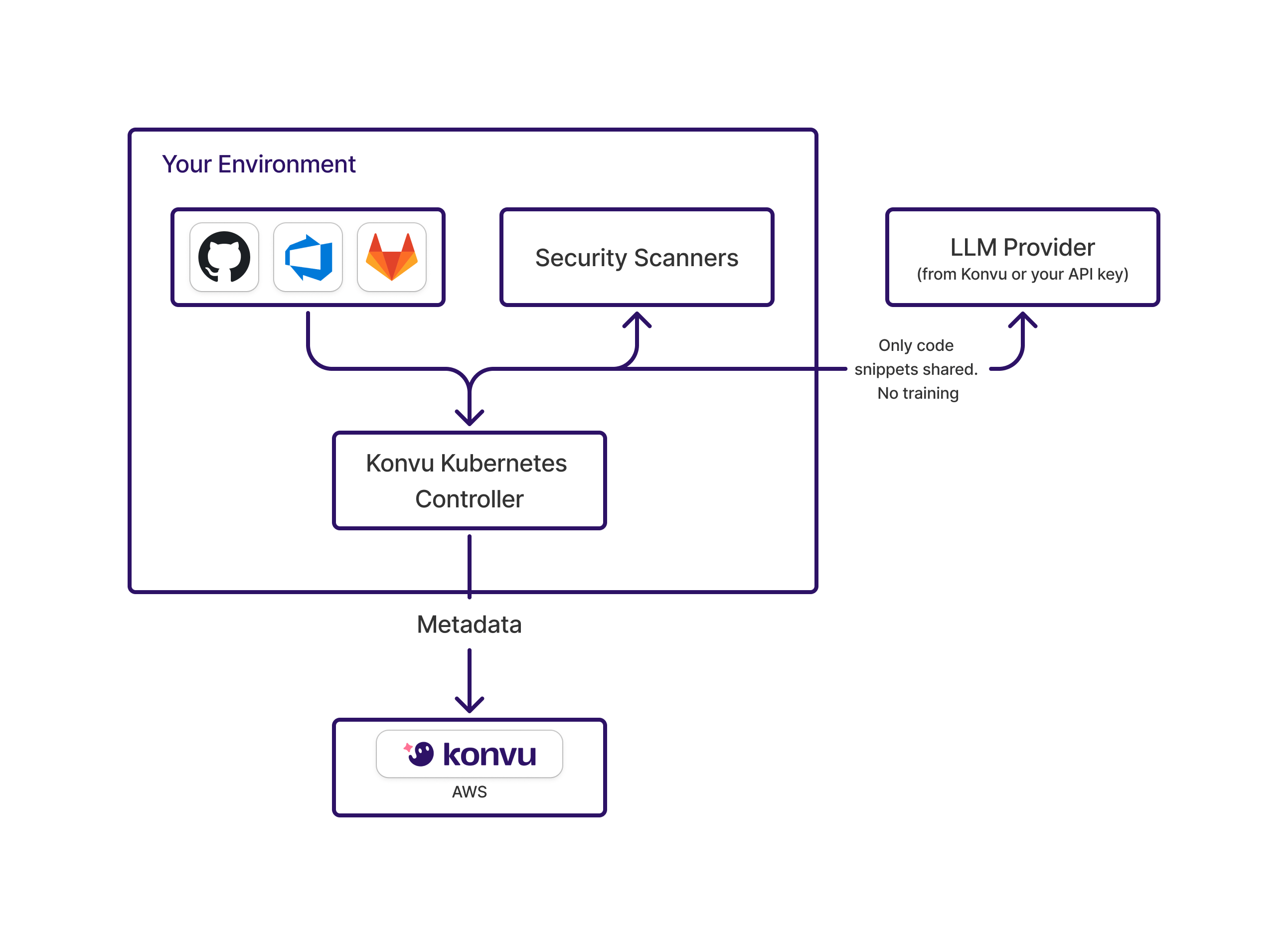
- Konvu K8s controller runs inside your environment
- Connects to your GitHub/GitLab and scanners within your network
- Konvu never has access to your code
- Bring your own LLM API key if you have an enterprise agreement
- Only metadata (decisions, evidence) flows to Konvu cloud
Cloud analysis
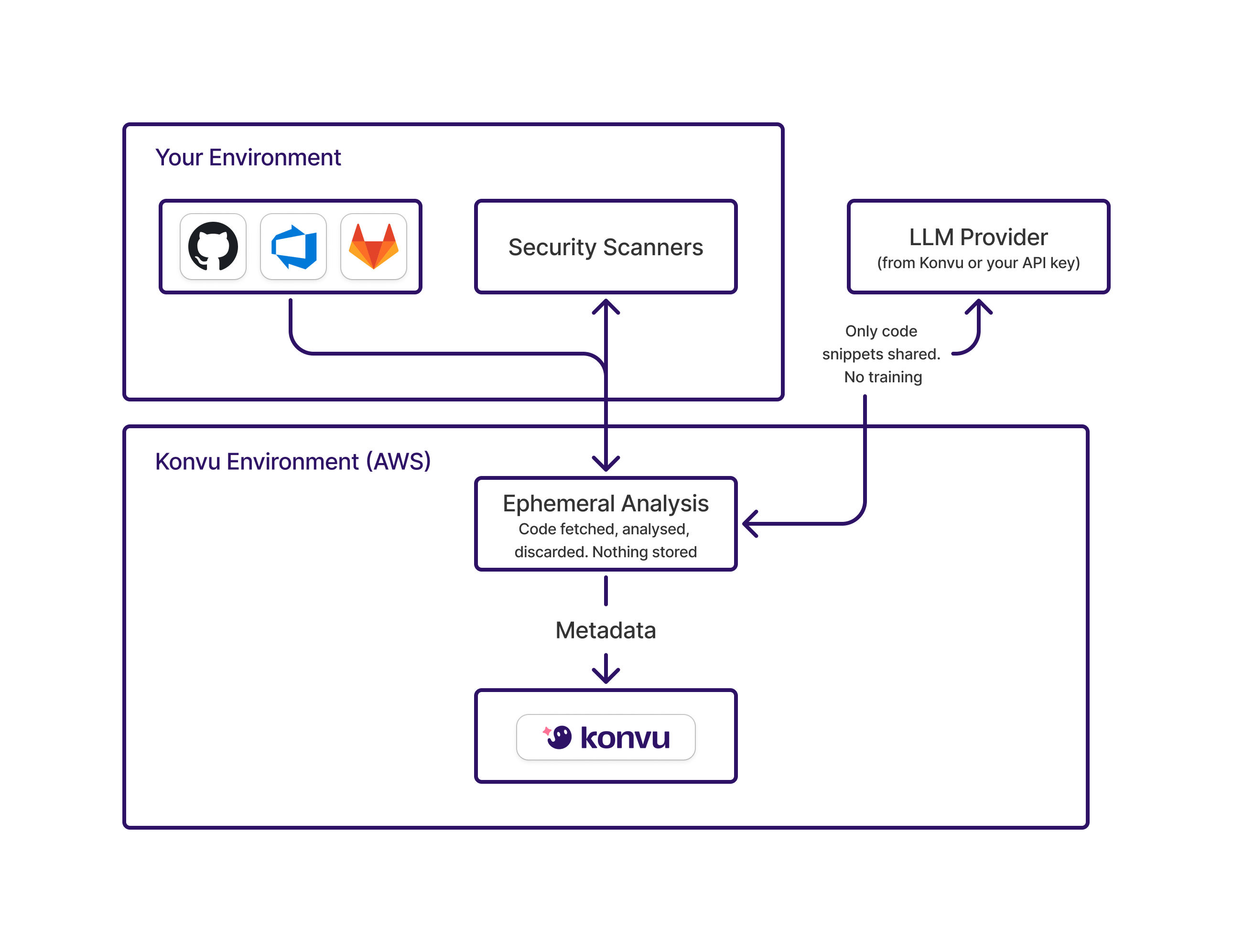
- Code fetched into Konvu's AWS environment for analysis
- Single-tenant analysis: one dedicated analysis engine per customer
- Ephemeral: code analyzed then discarded. Nothing stored
- Code snippets sent to LLM for exploitability analysis
- Only metadata (decisions, evidence) persisted in Konvu
What happens to your data
A concrete accounting of every data type, where it goes, and how long it lives.
| Data type | Self-hosted | Cloud analysis | Retention |
|---|---|---|---|
| Source code | Stays in your environment. Konvu never has access. | Fetched for ephemeral analysis, then discarded | None |
| Code snippets (sent to LLM) | Sent from your environment to LLM | Sent from Konvu environment to LLM | Zero. Contractual no-retention |
| Scanner findings | Processed in your environment | Processed in Konvu environment | Retained for ongoing triage |
| Triage decisions & evidence | Stored in Konvu | Stored in Konvu | Retained for audit trail |
| PII / end-user data | Never accessed | Never accessed | N/A |
How we use LLMs responsibly
Zero data retention
Contractual agreements with all LLM providers. Your data is not used for training, fine-tuning, or model improvement.
Minimal context window
Only the specific code snippet relevant to a finding is sent for analysis, not your full codebase.
Customer-managed keys
In self-hosted mode, if you have an enterprise agreement with an LLM provider, you can use your own API keys.
Multiple provider support
Our architecture supports multiple LLM providers. We select the best model for each analysis task.
Infrastructure and compliance
For the full picture, visit our Trust Center to access our SOC 2 report, pre-filled questionnaires, and policies.
SOC 2 Type II
Audited by Johanson Group. Report available through our Trust Center.
AWS infrastructure
Production workloads run on AWS.
GDPR compliant
Data Processing Addendum available. Subprocessor list maintained. EU data subject rights supported. See our Privacy Policy for full details.
Encryption
Data encrypted in transit and at rest.
External penetration testing
Annual third-party penetration testing of infrastructure and application layers.
Access control
Role-based access control with least privilege. MFA required for all internal access.
Internal security tooling
We run EDR, SCA, SAST, and cloud security scanners on our own infrastructure. We practice what we preach.
Vulnerability disclosure
Report vulnerabilities to security@konvu.com. See our security.txt.
Frequently asked questions
For any other questions, reach out to security@konvu.com. We will get back to you promptly.